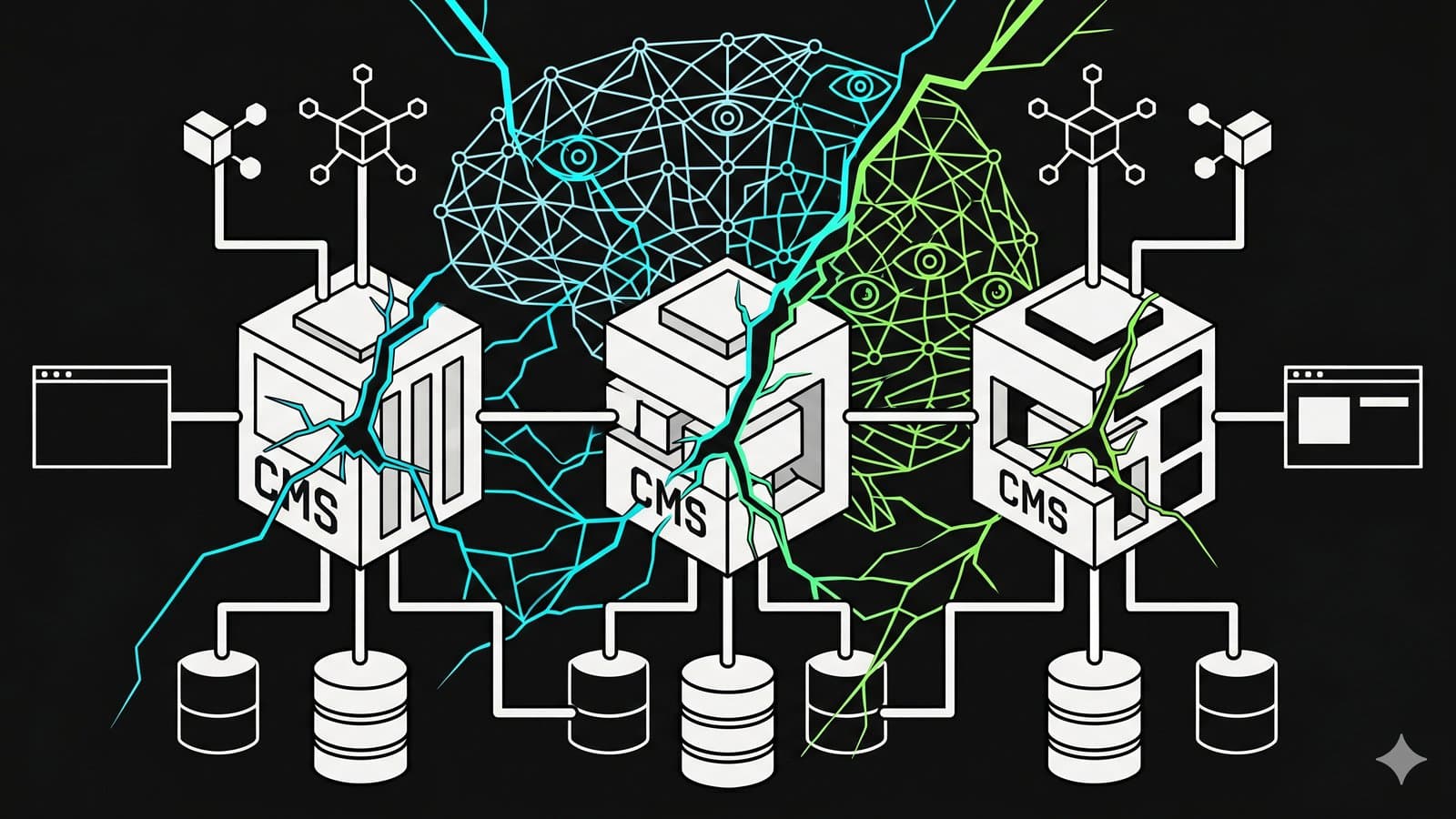
An AI model found thousands of zero-day vulnerabilities across every major browser and operating system — some hiding for over two decades. On April 8, 2026, Anthropic announced Claude Mythos Preview alongside Project Glasswing, a $100M cybersecurity initiative. The Mythos AI security findings hit enterprise CMS stacks hard: TLS library flaws affect every .NET application handling HTTPS, kernel-level privilege escalations compromise the Windows and Linux servers running Sitecore, Umbraco, and Optimizely, and browser sandbox escapes put every authenticated CMS backoffice session at risk.
I manage CMS implementations for enterprise clients across all three platforms. Here's the platform-specific checklist I'm running right now, and what every CMS team should prioritize before the 90-day public disclosure window opens in July 2026.
What Mythos Found and Why CMS Teams Should Care
Mythos is Anthropic's most capable AI model. It wasn't built for security — but its code reasoning capabilities made it extraordinarily effective at chaining exploitable vulnerabilities. The findings relevant to enterprise CMS stacks:
| Finding | CMS Impact |
|---|---|
| Browser sandbox escapes | Chained four vulnerabilities to escape both renderer and OS sandboxes. Every CMS backoffice session (Sitecore /sitecore/admin/, Umbraco /umbraco/, Optimizely /episerver/) becomes an attack vector if the editor's browser is unpatched. |
| TLS/AES-GCM flaws | .NET apps on Linux/Kestrel use OpenSSL directly. Self-hosted CMS instances with Kestrel reverse proxies are exposed. Windows IIS uses SChannel (not OpenSSL), but HttpClient calls to external APIs may route through vulnerable TLS stacks. |
| Linux kernel privilege escalation | Multiple chains affecting production servers. Any self-hosted CMS on Linux (common for Umbraco 10+ on Kestrel, containerized Sitecore XM Cloud builds) needs kernel patches. |
| Windows Server vulnerabilities | Kernel-level and HTTP.sys flaws affect IIS-hosted Sitecore 9-10, Umbraco, and Optimizely CMS 11-12. |
| 16-year-old FFmpeg bug | CMS media pipelines using FFmpeg for video transcoding or thumbnail generation are exposed. Crafted file uploads are the attack vector. |
The 90x improvement in exploit success rate between Opus 4.6 and Mythos (2 successes vs. 181 on Firefox exploit development) signals that AI-assisted vulnerability discovery now outpaces manual security research. Enterprise CMS platforms carry large dependency trees and legacy code — exactly the type of surface area Mythos excels at analyzing.
Sitecore: What to Patch and Harden Now
Sitecore's attack surface depends heavily on which generation you're running.
Sitecore 9.x–10.x (.NET Framework 4.8 / IIS)
Telerik UI is your top priority. Sitecore historically bundled Telerik UI for ASP.NET AJAX, which has a well-documented deserialization RCE history (CVE-2017-9248, CVE-2019-18935). If your Telerik.Web.UI.DialogParametersEncryptionKey is weak or default, an attacker with the capabilities Mythos demonstrates could chain this with the newly-discovered IIS/HTTP.sys vulnerabilities for full server compromise.
<!-- web.config — verify Telerik keys are rotated and strong -->
<appSettings>
<!-- ROTATE these keys. Default or weak values are exploitable -->
<add key="Telerik.Web.UI.DialogParametersEncryptionKey" value="YOUR-STRONG-KEY-HERE" />
<add key="Telerik.Upload.ConfigurationHashKey" value="YOUR-STRONG-KEY-HERE" />
</appSettings>Additional hardening:
- Block public access to
/sitecore/admin/and/sitecore/login/via IP allowlisting or VPN - Audit
Newtonsoft.Jsonusage — anyTypeNameHandlingsetting other thanNoneenables deserialization attacks - Patch Windows Server and IIS immediately against the disclosed HTTP.sys vulnerabilities
- Review
Sitecore.configfor hardcodedHashAlgorithmkeys and rotate them - Restrict media library upload extensions — Sitecore's default allows types that can trigger server-side processing vulnerabilities
Sitecore XM Cloud
XM Cloud shifts the server-side risk to Sitecore's managed infrastructure, but your rendering host (Next.js on Vercel or self-hosted) still needs attention:
- Update your Next.js rendering host dependencies
- Audit any middleware that processes media from the Sitecore CDN
- Review Experience Edge API keys and scope permissions
Umbraco: Backoffice and Media Pipeline Risks
Umbraco 10-14 runs on .NET 6/7/8, which means Kestrel is the default web server — and OpenSSL TLS vulnerabilities apply directly when hosted on Linux.
Critical Items
ImageSharp is your FFmpeg equivalent. Umbraco uses ImageSharp for server-side image processing. Pre-3.x versions had memory exhaustion vulnerabilities (CVE-2022-24795) triggered by crafted image uploads. With Mythos demonstrating the ability to find similar media processing bugs at scale, update ImageSharp to the latest version and validate that your upload validation rejects malformed images before they hit the processing pipeline.
// Startup.cs — restrict upload file types and sizes
services.AddUmbraco(_env, _config)
.AddBackOffice()
.AddWebsite()
.Build();
// In appsettings.json — tighten allowed upload extensions
// Remove any media types you don't need
{
"Umbraco": {
"CMS": {
"Content": {
"AllowedUploadedFileExtensions": ["jpg", "jpeg", "png", "gif", "webp", "svg", "pdf"]
}
}
}
}Backoffice hardening:
- Umbraco's backoffice at
/umbraco/has no built-in rate limiting by default — add brute-force protection via middleware or a WAF - TinyMCE (the rich text editor) has had XSS vectors in older versions (CVE-2024-38356). Update to the version bundled with your Umbraco LTS release
- If running on Linux/Kestrel: patch the kernel against Mythos-discovered privilege escalation chains
- If running on Windows/IIS: patch HTTP.sys and the Windows kernel
Umbraco Cloud vs Self-Hosted
Umbraco Cloud (Azure-managed) handles OS patching and TLS termination. Self-hosted instances inherit every OS and runtime vulnerability. If you're self-hosted, the Mythos findings add urgency to evaluating managed hosting — or at minimum, automating your patch pipeline.
Optimizely: DXP Cloud vs Self-Hosted Exposure
The security gap between Optimizely's DXP Cloud and self-hosted CMS 11/12 has never been wider.
Self-Hosted CMS 11 (.NET Framework 4.8)
CMS 11 is the legacy surface. It runs on .NET Framework 4.8, typically IIS on Windows Server. Every Windows kernel and HTTP.sys vulnerability Mythos found applies here.
Priority actions:
- Patch Windows Server immediately — the privilege escalation chains Mythos discovered grant kernel-level access
- Audit
Newtonsoft.JsonwithTypeNameHandling— same deserialization risk as Sitecore - Review
/episerver/admin UI exposure. Block public access via network rules - Audit scheduled jobs endpoints — these accept remote execution triggers if misconfigured
- Check
Microsoft.Data.SqlClientversion (pre-5.1.4 has known vulnerabilities)
Self-Hosted CMS 12 (.NET 6+)
CMS 12 on .NET 6+ is more modern but still self-managed:
// Program.cs — add security headers middleware
app.Use(async (context, next) =>
{
context.Response.Headers.Append("X-Content-Type-Options", "nosniff");
context.Response.Headers.Append("X-Frame-Options", "DENY");
context.Response.Headers.Append("Referrer-Policy", "strict-origin-when-cross-origin");
context.Response.Headers.Append("Permissions-Policy", "camera=(), microphone=(), geolocation=()");
context.Response.Headers.Append(
"Content-Security-Policy",
"default-src 'self'; script-src 'self'; frame-ancestors 'none'");
await next();
});- Audit the Optimizely add-on marketplace packages you've installed — these are community-contributed and not security-audited by Optimizely
- Review Content Delivery API authorization scopes. The default configuration is often more permissive than needed
- Check visitor group criteria for injection vectors
DXP Cloud
DXP Cloud manages OS patching, TLS termination, and includes a WAF. The Mythos findings are largely handled by Optimizely's infrastructure team. Your responsibility: audit application-level code, add-on packages, and Content Delivery API configurations.
Cross-Platform: The Shared .NET Attack Surface
Regardless of which CMS you run, these .NET-specific concerns apply to all three:
NuGet Packages to Audit Now
| Package | Risk | Action |
|---|---|---|
Newtonsoft.Json | Deserialization RCE when TypeNameHandling != None | Audit all usages, set to None where possible |
System.Text.Json | Pre-8.0.5 has known vulnerabilities | Update to latest |
Microsoft.Data.SqlClient | Pre-5.1.4 has SQL injection vectors | Update immediately |
Microsoft.IdentityModel.* | Pre-7.x had token validation bypasses | Update all identity packages |
System.Security.Cryptography.Xml | XML signature wrapping attacks | Update and audit XML processing |
Automate Vulnerability Scanning
Running dotnet list package --vulnerable across 15 client solutions manually won't scale. Automate it.
# Audit all .NET projects in a client directory
for sln in ~/clients/*/*.sln; do
echo "=== $(basename "$(dirname "$sln")") ==="
dotnet list "$sln" package --vulnerable --include-transitive 2>/dev/null | grep -E "(Critical|High)"
doneTooling for .NET CMS stacks:
- GitHub Dependabot — Enable NuGet source scanning on all repos
- Snyk — Supports .NET and NuGet with transitive dependency analysis
dotnet-outdated— CLI tool for checking outdated NuGet packages across solutions- OWASP Dependency-Check — Integrates with Azure DevOps and GitHub Actions
How to Prioritize: A Risk-Based Decision Matrix
Not every CMS instance carries the same risk. Use this matrix to triage which systems to patch first.
| Factor | Higher Risk | Lower Risk |
|---|---|---|
| Hosting model | Self-hosted on bare metal or unmanaged VMs | Cloud-managed (XM Cloud, Umbraco Cloud, DXP Cloud) |
| Runtime | .NET Framework 4.8 (Sitecore 9-10, Optimizely CMS 11) | .NET 6+ (Umbraco 10-14, Optimizely CMS 12) |
| Admin panel exposure | /sitecore/admin/, /umbraco/, /episerver/ publicly accessible | Admin restricted via VPN or IP allowlist |
| Dependency age | Telerik UI, ImageSharp pre-3.x, Newtonsoft.Json with TypeNameHandling | Current LTS packages, no known vulnerable transitive deps |
| OS patching cadence | Monthly or slower | Automated weekly with rollback capability |
| Media processing | FFmpeg or ImageSharp processing user uploads | No server-side media processing or uploads restricted to trusted editors |
Patch Order
Tier 1 — Patch this week: Self-hosted .NET Framework 4.8 instances with publicly exposed admin panels. These combine the oldest runtime, the widest OS attack surface, and the most exploitable entry points (Telerik deserialization, HTTP.sys). Sitecore 9.x and Optimizely CMS 11 fall here.
Tier 2 — Patch within two weeks: Self-hosted .NET 6+ instances on Linux/Kestrel. The runtime is modern, but the Mythos kernel privilege escalation chains and OpenSSL TLS flaws apply directly. Umbraco 10-14 on Linux and Optimizely CMS 12 on Kestrel fall here.
Tier 3 — Patch within 30 days: Self-hosted .NET 6+ on Windows/IIS with admin panels behind VPN. The attack surface is smaller — Windows SChannel handles TLS (not OpenSSL), and the admin panel isn't publicly reachable. Still patch Windows Server and audit NuGet dependencies.
Tier 4 — Audit application code only: Cloud-managed platforms (XM Cloud, Umbraco Cloud, DXP Cloud). The provider handles OS, TLS, and infrastructure patching. Your responsibility is application-level: third-party packages, API authorization scopes, and upload validation.
When This Doesn't Apply
Managed cloud platforms absorb most of the risk. If you're on Sitecore XM Cloud, Umbraco Cloud, or Optimizely DXP Cloud, the OS-level and TLS-level vulnerabilities Mythos discovered are patched by the platform provider. Your responsibility narrows to application-level code, third-party packages, and API configurations.
Static/headless rendering hosts are lower risk. If your CMS uses a headless architecture with a static frontend (Next.js on Vercel, for example), the server-side CMS attack surface is isolated from the public-facing site. The CMS backoffice still needs hardening, but the blast radius of a compromise is contained.
This applies to everyone else. Self-hosted CMS instances on unpatched Windows Server or Linux, legacy .NET Framework 4.8 applications with known vulnerable dependencies, exposed admin panels without IP restrictions — the Mythos findings make this posture untenable. The window between disclosure and exploitation is shrinking from months to days.
Conclusion
Mythos demonstrated that AI can find and chain exploits across operating systems, browsers, TLS libraries, and server software at a rate 90x faster than the previous generation. For enterprise CMS teams running Sitecore, Umbraco, or Optimizely, the attack surface is broad: admin panels, media processing pipelines, deserialization endpoints, and the OS underneath it all.
Key Takeaways:
- Sitecore teams: Rotate Telerik encryption keys, block
/sitecore/admin/publicly, auditNewtonsoft.JsonTypeNameHandling, and patch Windows Server - Umbraco teams: Update ImageSharp, add backoffice brute-force protection, patch TinyMCE, and address Linux kernel vulnerabilities if on Kestrel
- Optimizely teams: Audit add-on packages, restrict Content Delivery API scopes, and patch self-hosted Windows/IIS instances immediately
- All .NET CMS teams: Run
dotnet list package --vulnerable --include-transitiveacross every solution. Automate it with Dependabot or Snyk. Set a hard patch deadline of June 30, 2026 — before the 90-day Glasswing disclosures go public - Evaluate managed hosting: The security gap between self-hosted and cloud-managed CMS has never been wider. If you're still self-hosting, the operational cost of staying patched post-Mythos may exceed the cost of migration
The Glasswing partner list — AWS, Apple, Google, Microsoft, CrowdStrike — tells you how seriously the industry is taking this. Match that energy across your CMS portfolio.
If you're exploring how AI capabilities are reshaping development workflows beyond security, check out how Claude Managed Agents replaces DIY agent infrastructure and multi-agent pipeline architectures. The same AI capability curve driving Mythos is transforming how we build software — understanding both sides matters.
You Might Also Like

Building a Claude Code Plugin Marketplace for CMS Analysis
Replace generic linters with 50 platform-specific rules per CMS. Specialized Claude Code plugins outperform general agents for Sitecore and Umbraco analysis.

The Agent Operating System: Multi-Agent Pipelines with Claude
Map OS abstractions to Claude Managed Agents architecture and build a three-agent auto-PR pipeline that plans, codes, and reviews autonomously.

Claude Managed Agents: The End of DIY Agent Infrastructure
Discover how Claude Managed Agents replaces months of custom agent infrastructure with a decoupled architecture that cuts time-to-first-token 60%.
Comments
Loading comments...